

Submissions
The Harvard International Review welcomes submissions from contributing authors. Please include your full name, any affiliations with Harvard University or other institutions and organizations relevant to the content of your article, and an evening or mobile phone number so that you can be contacted if your piece is chosen for publication.
Submissions to the HIR must be previously unpublished. Though we encourage contributors to use prior articles and columns to spark their thinking, submissions that directly reference, quote, or paraphrase prior articles will not be chosen for publication.
We do not publish articles written on behalf of an organization, club or group, whether at Harvard, in Cambridge, or on a national or international scale. We furthermore strongly discourage groups of people from submitting articles together except when absolutely necessary. In such cases, we will likely restrict primary authorship to one individual. As a policy, we do not permit anonymous submissions.
The HIR reserves the right to edit all submissions prior to publication, though authors will be contacted regarding any major changes. The HIR is responsible for all article titles.
All submissions must be edited to adhere to our writing and style guide . The HIR only accepts " Global Notebook " articles from contributing authors; we do not accept time-sensitive contributions. All submissions must be pre-formated to meet the HIR style guide. Submissions must also include images, captions, and sourcing as per the style guide. Failure to follow these guidelines will result in your submission being archived without response. Please be aware that a small fraction of submissions are chosen for publication.
Submissions welcome to the editors via [email protected].

- Sponsorship
- The MITIR Approach
- How to Submit
- Advertising
- Originality : The paper must contain original and unpublished work.
- File Format : Papers should be submitted as Microsoft Word files (*.doc) or as Rich Text Format files (*.rtf).
- Length : Maximum words of possible submission categories: - Traditional Essays (4000) - Original Data-Centered Research (2000, free of all technical jargon) - Case Studies (2000) - Interviews (1500) (e.g., medical treatments) for the resolution of a global problem - Field Reports (1500): For those who can impart an outsider’s perspective on global problems and what is being done about them - Work-in-Progress (1200): For those who are pioneering new technologies or services - Opinion Editorials (800) - Photo Essays (maximum: 10 photographs).
- Contact Information : A separate page should list: - Name(s) of the author(s) - Address - Telephone (and fax number) - E-mail address - Institutional affiliation.
- Abstract : The first page of the actual article should contain the following information: - Title - Name(s) of the author(s) - An abstract of no more than 100 words - Word count of the article.
- Accuracy : Facts in submissions will be reviewed to ensure accuracy.
- References should be included.
- Figures should not be copyrighted.
Please submit your work to [email protected] .
Note : After initial submission, writers whose articles are being considered for publication may be asked to resubmit their articles according to more specific guidelines.
Unfortunately we don't fully support your browser. If you have the option to, please upgrade to a newer version or use Mozilla Firefox , Microsoft Edge , Google Chrome , or Safari 14 or newer. If you are unable to, and need support, please send us your feedback .
We'd appreciate your feedback. Tell us what you think! opens in new tab/window
2. Prepare your paper for submission
Preparing your paper.
Read the guide for authors, which you can find on the journal’s homepage opens in new tab/window . It contains specific requirements related to ethics, open access options, copyright and funding body agreements. It also provides guidelines for preparing your paper, covering:
Article structure
Highlights and keywords
Accepted formats for artwork, data sources and video
Don’t let your language get you rejected
Poor English is one of the most common reasons for rejection. You can avoid this by having your manuscript proofread or edited. Reach the highest standards with Elsevier's Author Services opens in new tab/window :
Language editing and quality services opens in new tab/window ensure that your manuscript is free of grammatical and spelling errors within five business days
Adding research data
As a researcher, you are increasingly encouraged, and sometimes even required, to make your research data available, accessible, discoverable and usable.
As an Elsevier author, when submitting your article, you can choose to store your data in a repository like Mendeley Data opens in new tab/window , in order to make your dataset independently citable, and link it with your article.
You can also choose to submit a brief, peer-reviewed data article. Your data article will be published in the dedicated, open access journal Data in Brief opens in new tab/window and will be indexed, as well as linked, with your original research article.
Be sure to cite your research data in your article. This ensures you receive credit for your work, while making your research data accessible, giving your readers deeper insights and supporting their work. Find out more .
Data visualizations
You can enrich your article with interactive visualizations and provide context by adding references to (external) information sources, such as high-resolution imagery viewers, geospatial maps and 3D models. This enhances your research data and makes your key findings easily comprehensible for your readers. Find out more .
Data statement
Elsevier journals and many others provide guidelines on data sharing. There can be reasons why you are not able to share your research data, for example, due to confidentiality. In this case, you are encouraged to submit a data statement which will appear next to your article and state the reason why your dataset is not linked to your article.
Find out more about Elsevier’s author resources .
Postdoc free access program
For scholars who recently received their PhDs and currently do not have a research position, we are pleased to offer unlimited complimentary access to all our journals and books on ScienceDirect opens in new tab/window , for up to 12 months * . This program allows those who qualify to have access to scientific journals and books in their field. Read more about the program
- Research Process
- Manuscript Preparation
- Manuscript Review
- Publication Process
- Publication Recognition
- Language Editing Services
- Translation Services

How to Submit a Paper for Publication in a Journal
- 4 minute read
- 100.1K views
Table of Contents
Whether you’ve done it before, or not, submitting a paper for publication in a journal is, to say the least, a process that brings great anxiety and stress. After all your hard work for many months, or even years, recognition is finally at your grasp. That is why there no room for mistakes.
What to Expect of the Scientific Publishing Process
If you are a beginner, you might be struggling to know exactly what to do. After all, it is a step-by-step process, sometimes with a lot of players and paperwork involved; it’s not always evident what to do next. An excellent, high-quality manuscript is the best way to give a good impression from the beginning, putting your paper on the right track for a successful submission. At Elsevier, with our Language Editing services , we not only revise your manuscript, but guarantee there are no text errors.
If, on the other hand, you have already published articles, you might have enough experience to know that each paper submission in a journal is different. Either the journal is different, or the context has changed, or the peers are new. You never know what can go right or wrong, other than the variable that lies under your control – that the manuscript is error-free and spot-on for successful acceptance. In this case, you might consider Elsevier’s professional Language Editing services to amend your text to the target journal’s requirements, helping you focus on other projects.
Scientific Paper Submission. Are you ready? Let’s go!
For many researchers, putting their paper through the professional journal submission process is stressful. Here is a simple to-do list which might help you go through all of it with some peace of mind:
- Use an external editing service, such as Elsevier’s Author Services if you need assistance with language.
- Free e-learning modules on preparing your manuscript can be found on Researcher Academy.
- Mendeley makes your life easier by helping you organize your papers, citations and references, accessing them in the cloud on any device, wherever you are.
- Do not rush submitting your article for publication Carefully re-read and revise your manuscript. Re-reading is essential in the research field and helps identify the most common problems and shortcomings in the manuscript, which might otherwise be overlooked. Often, reading your text out loud will uncover more errors than reading silently to yourself. If you are doubtful about the quality of your text, consider Elsevier’s Professional Language Editing services . Our professional team is trained to provide you with an optimal text for successful submission.
- Read the journal’s aims and scope to make sure they match your paper.
- Check whether you can submit – some journals are invitation only.
- Use the journal’s metrics to measure its impact. In fact, you can also check other additional info – like speed and reach to understand if it’s the right one for you.
- If you’re a post doc, check out our free access program.
- Read the aims and scope and author guidelines of your target journal carefully Once you think your manuscript is ready for submission, the next important step is to read the aims and scope of the journals in your target research area. Doing so will improve the chances of having your manuscript accepted for publishing.
- Submit a cover letter with the manuscript Never underestimate the importance of a cover letter addressed to the editor or editor-in-chief of the target journal. A good cover letter should underline 3 main aspects: the main theme of the paper, its originality/novelty and the relevance of the manuscript to the target journal.
- Make a good first impression with your title and abstract The title and abstract are incredibly important components of a manuscript as they are the first elements a journal editor sees. They create interest and curiosity about the whole work.
Now, what happens if your paper gets rejected by the journal ? It is, by no means, the end of the world. There are very real steps you can take to ultimately get published in a reputable journal.
The Science of Article Publishing
Article publishing is every researcher’s aim. It brings visibility and recognition, essential factors for those who intend to build a full career in research. However, most scientists feel handicapped or lost when it comes to conveying their findings or ideas to others. For many, it can be difficult to re-format a certain type of text to another, be aware of formatting requirements and translate their work into visually appealing outcomes. Additionally, keeping track of all the steps needed to submit an article for publication can be overwhelming and take too much time that could be spent doing new research.
At Elsevier, we believe everyone should be doing what they do best: in this case, leave research for scientists and leave the science of turning the best ideas into excellent quality text to our professionals.
Language Editing Services by Elsevier Author Services:
Find more about How to Submit a Paper for Publication in a Journal on Pinterest:

How to Write a Journal Article from a Thesis

Looking for Medical Editing Services
You may also like.

How to Make a PowerPoint Presentation of Your Research Paper

What is a Good H-index?

What is a Corresponding Author?
Input your search keywords and press Enter.
- Insights blog
Research your publishing options
Take the time to explore the journals in your field, to choose the best fit for your research. Find a journal that serves the audience you’re trying to reach, and whose aims and scope match your approach. You might also have choices to make about different publishing options, including open access.
Discover more about choosing the right journal
Draft your article
When you’ve chosen the journal you want to submit to, you’re ready to start drafting your paper. What should you be thinking about before you start writing and how can you maximize your chances of getting published?
Get advice on writing your paper

Read the instructions for authors
The instructions for authors include essential information on what you need to do to submit to your chosen journal. Follow these guidelines and you’ll know that the journal’s editorial team have everything they need to consider your article for publication.
Learn how to use the instructions for authors
Make your submission
So, you’ve done your research, chosen your target journal, written your paper, and are about to submit. Time for one final check to make sure you’ve got everything ready before heading to the journal’s submission system.
Get prepared to submit your paper

Peer review
If the journal editor thinks your article has potential for publication, they will send it out to be reviewed by two or three experts in the field. This can be a daunting prospect, but peer review is a fundamental part of getting published and can be a great opportunity to access constructive feedback on your work.
Read our comprehensive guide to peer review
Making revisions
Following peer review, you may be asked to make revisions to your article and resubmit. Take time to read through the editor and reviewers’ advice, and decide what changes you’ll make to your article. Taking their points on board will help to ensure your final article is as robust and impactful as possible.
Get guidance on revising and resubmitting
Your article is accepted
The next step is production. Copy editing begins, and we’ll contact you with your proofs. You’ll also sign a publishing agreement. If you submitted to an Open Select journal, now is the time to choose whether to publish your article open access.
Find out what happens when your article is in production
Promoting your published work
Promoting your published article is a team effort. Taylor & Francis works hard to maximize the discoverability of your work, and we’ve got lots of advice to help you share your work and amplify its impact.
Learn how to get the most from your published article
Trending topics
Boost your research career by signing up to Research Insights and receive free expert guidance on the publishing process.
Need help getting published?
Thinking about where to submit your paper? Our comprehensive guide to choosing a journal is here to help.
Free guide to choosing a journal

Call for papers in your subject area

Journals regularly ‘call for papers’, asking for submissions within a particular field or topic. Answering these is a great way to get published, making sure your research fits the journal’s aims and scope. Simply select your subject area with our handy tool to get started.
Browse upcoming events for researchers

We are delighted to share the details of our upcoming events for researchers, hosted by Taylor & Francis. Take a look at the events happening and register your place for those which are relevant to you and your research.
What do you consider important in a high-quality journal?

What factors help you decide if a journal is a good venue to publish your article, or is a reliable source of the latest research?
Let us know what is important to you in our journal quality survey.
How has our partnership with Jisc accelerated the transition to open access?

We are pleased to share a new report published by Taylor & Francis that explores the first two years of our open access partnership with the Jisc consortium. It details how the partnership has boosted the global impact of research from UK institutions.
Read our new report on how to create an enabling environment for translational research practices

How to support translational research design principles throughout the knowledge journey? Who needs to be involved?
Taylor & Francis partners with EASSH and EATRIS to explore ways to support cross disciplinary and cross sectoral collaboration.
- SpringerLink shop
Electronic submission
Electronic submission substantially reduced the editorial processing and reviewing times and shortened overall publication times. To submit to the journal of your choice, click the Submit Manuscript button on the journal's homepage.
The link leads you directly to the submission system used by that journal, which is either Editorial Manager, Manuscript Central or Snapp.
Include your ORCID iD
This ID uniquely attaches your identity to your research work, such as your articles and citations. The result: no more confusion because another researcher has the same or a similar name!
To register a new or existing ORCID number, log in to the editorial system and select 'Edit My Account' or 'Update My Information' from the menu.
You can read more about ORCID and its benefits here .
Add your research funding source
It will give your article additional visibility.
Our submission systems will offer the option to include your funding source in a standardized way. In most cases you will be able to choose your funder from the given list. Otherwise, please add it manually.
The funding information will be published as searchable meta-data for the accepted article.
It will be made publicly available through Crossref's funding data search and your article can be found by anyone who looks for your funder’s name.
Further reading: The Crossref Funder Registry
Back to top of Submission
Reviewing and acceptance
Home » How to Publish a Research Paper – Step by Step Guide
How to Publish a Research Paper – Step by Step Guide
Table of Contents

Publishing a research paper is an important step for researchers to disseminate their findings to a wider audience and contribute to the advancement of knowledge in their field. Whether you are a graduate student, a postdoctoral fellow, or an established researcher, publishing a paper requires careful planning, rigorous research, and clear writing. In this process, you will need to identify a research question , conduct a thorough literature review , design a methodology, analyze data, and draw conclusions. Additionally, you will need to consider the appropriate journals or conferences to submit your work to and adhere to their guidelines for formatting and submission. In this article, we will discuss some ways to publish your Research Paper.
How to Publish a Research Paper
To Publish a Research Paper follow the guide below:
- Conduct original research : Conduct thorough research on a specific topic or problem. Collect data, analyze it, and draw conclusions based on your findings.
- Write the paper : Write a detailed paper describing your research. It should include an abstract, introduction, literature review, methodology, results, discussion, and conclusion.
- Choose a suitable journal or conference : Look for a journal or conference that specializes in your research area. You can check their submission guidelines to ensure your paper meets their requirements.
- Prepare your submission: Follow the guidelines and prepare your submission, including the paper, abstract, cover letter, and any other required documents.
- Submit the paper: Submit your paper online through the journal or conference website. Make sure you meet the submission deadline.
- Peer-review process : Your paper will be reviewed by experts in the field who will provide feedback on the quality of your research, methodology, and conclusions.
- Revisions : Based on the feedback you receive, revise your paper and resubmit it.
- Acceptance : Once your paper is accepted, you will receive a notification from the journal or conference. You may need to make final revisions before the paper is published.
- Publication : Your paper will be published online or in print. You can also promote your work through social media or other channels to increase its visibility.
How to Choose Journal for Research Paper Publication
Here are some steps to follow to help you select an appropriate journal:
- Identify your research topic and audience : Your research topic and intended audience should guide your choice of journal. Identify the key journals in your field of research and read the scope and aim of the journal to determine if your paper is a good fit.
- Analyze the journal’s impact and reputation : Check the impact factor and ranking of the journal, as well as its acceptance rate and citation frequency. A high-impact journal can give your paper more visibility and credibility.
- Consider the journal’s publication policies : Look for the journal’s publication policies such as the word count limit, formatting requirements, open access options, and submission fees. Make sure that you can comply with the requirements and that the journal is in line with your publication goals.
- Look at recent publications : Review recent issues of the journal to evaluate whether your paper would fit in with the journal’s current content and style.
- Seek advice from colleagues and mentors: Ask for recommendations and suggestions from your colleagues and mentors in your field, especially those who have experience publishing in the same or similar journals.
- Be prepared to make changes : Be prepared to revise your paper according to the requirements and guidelines of the chosen journal. It is also important to be open to feedback from the editor and reviewers.
List of Journals for Research Paper Publications
There are thousands of academic journals covering various fields of research. Here are some of the most popular ones, categorized by field:
General/Multidisciplinary
- Nature: https://www.nature.com/
- Science: https://www.sciencemag.org/
- PLOS ONE: https://journals.plos.org/plosone/
- Proceedings of the National Academy of Sciences (PNAS): https://www.pnas.org/
- The Lancet: https://www.thelancet.com/
- JAMA (Journal of the American Medical Association): https://jamanetwork.com/journals/jama
Social Sciences/Humanities
- Journal of Personality and Social Psychology: https://www.apa.org/pubs/journals/psp
- Journal of Consumer Research: https://www.journals.uchicago.edu/journals/jcr
- Journal of Educational Psychology: https://www.apa.org/pubs/journals/edu
- Journal of Applied Psychology: https://www.apa.org/pubs/journals/apl
- Journal of Communication: https://academic.oup.com/joc
- American Journal of Political Science: https://ajps.org/
- Journal of International Business Studies: https://www.jibs.net/
- Journal of Marketing Research: https://www.ama.org/journal-of-marketing-research/
Natural Sciences
- Journal of Biological Chemistry: https://www.jbc.org/
- Cell: https://www.cell.com/
- Science Advances: https://advances.sciencemag.org/
- Chemical Reviews: https://pubs.acs.org/journal/chreay
- Angewandte Chemie: https://onlinelibrary.wiley.com/journal/15213765
- Physical Review Letters: https://journals.aps.org/prl/
- Journal of Geophysical Research: https://agupubs.onlinelibrary.wiley.com/journal/2156531X
- Journal of High Energy Physics: https://link.springer.com/journal/13130
Engineering/Technology
- IEEE Transactions on Neural Networks and Learning Systems: https://ieeexplore.ieee.org/xpl/RecentIssue.jsp?punumber=5962385
- IEEE Transactions on Power Systems: https://ieeexplore.ieee.org/xpl/RecentIssue.jsp?punumber=59
- IEEE Transactions on Medical Imaging: https://ieeexplore.ieee.org/xpl/RecentIssue.jsp?punumber=42
- IEEE Transactions on Control Systems Technology: https://ieeexplore.ieee.org/xpl/RecentIssue.jsp?punumber=87
- Journal of Engineering Mechanics: https://ascelibrary.org/journal/jenmdt
- Journal of Materials Science: https://www.springer.com/journal/10853
- Journal of Chemical Engineering of Japan: https://www.jstage.jst.go.jp/browse/jcej
- Journal of Mechanical Design: https://asmedigitalcollection.asme.org/mechanicaldesign
Medical/Health Sciences
- New England Journal of Medicine: https://www.nejm.org/
- The BMJ (formerly British Medical Journal): https://www.bmj.com/
- Journal of the American Medical Association (JAMA): https://jamanetwork.com/journals/jama
- Annals of Internal Medicine: https://www.acpjournals.org/journal/aim
- American Journal of Epidemiology: https://academic.oup.com/aje
- Journal of Clinical Oncology: https://ascopubs.org/journal/jco
- Journal of Infectious Diseases: https://academic.oup.com/jid
List of Conferences for Research Paper Publications
There are many conferences that accept research papers for publication. The specific conferences you should consider will depend on your field of research. Here are some suggestions for conferences in a few different fields:
Computer Science and Information Technology:
- IEEE International Conference on Computer Communications (INFOCOM): https://www.ieee-infocom.org/
- ACM SIGCOMM Conference on Data Communication: https://conferences.sigcomm.org/sigcomm/
- IEEE Symposium on Security and Privacy (SP): https://www.ieee-security.org/TC/SP/
- ACM Conference on Computer and Communications Security (CCS): https://www.sigsac.org/ccs/
- ACM Conference on Human-Computer Interaction (CHI): https://chi2022.acm.org/
Engineering:
- IEEE International Conference on Robotics and Automation (ICRA): https://www.ieee-icra.org/
- International Conference on Mechanical and Aerospace Engineering (ICMAE): http://www.icmae.org/
- International Conference on Civil and Environmental Engineering (ICCEE): http://www.iccee.org/
- International Conference on Materials Science and Engineering (ICMSE): http://www.icmse.org/
- International Conference on Energy and Power Engineering (ICEPE): http://www.icepe.org/
Natural Sciences:
- American Chemical Society National Meeting & Exposition: https://www.acs.org/content/acs/en/meetings/national-meeting.html
- American Physical Society March Meeting: https://www.aps.org/meetings/march/
- International Conference on Environmental Science and Technology (ICEST): http://www.icest.org/
- International Conference on Natural Science and Environment (ICNSE): http://www.icnse.org/
- International Conference on Life Science and Biological Engineering (LSBE): http://www.lsbe.org/
Social Sciences:
- Annual Meeting of the American Sociological Association (ASA): https://www.asanet.org/annual-meeting-2022
- International Conference on Social Science and Humanities (ICSSH): http://www.icssh.org/
- International Conference on Psychology and Behavioral Sciences (ICPBS): http://www.icpbs.org/
- International Conference on Education and Social Science (ICESS): http://www.icess.org/
- International Conference on Management and Information Science (ICMIS): http://www.icmis.org/
How to Publish a Research Paper in Journal
Publishing a research paper in a journal is a crucial step in disseminating scientific knowledge and contributing to the field. Here are the general steps to follow:
- Choose a research topic : Select a topic of your interest and identify a research question or problem that you want to investigate. Conduct a literature review to identify the gaps in the existing knowledge that your research will address.
- Conduct research : Develop a research plan and methodology to collect data and conduct experiments. Collect and analyze data to draw conclusions that address the research question.
- Write a paper: Organize your findings into a well-structured paper with clear and concise language. Your paper should include an introduction, literature review, methodology, results, discussion, and conclusion. Use academic language and provide references for your sources.
- Choose a journal: Choose a journal that is relevant to your research topic and audience. Consider factors such as impact factor, acceptance rate, and the reputation of the journal.
- Follow journal guidelines : Review the submission guidelines and formatting requirements of the journal. Follow the guidelines carefully to ensure that your paper meets the journal’s requirements.
- Submit your paper : Submit your paper to the journal through the online submission system or by email. Include a cover letter that briefly explains the significance of your research and why it is suitable for the journal.
- Wait for reviews: Your paper will be reviewed by experts in the field. Be prepared to address their comments and make revisions to your paper.
- Revise and resubmit: Make revisions to your paper based on the reviewers’ comments and resubmit it to the journal. If your paper is accepted, congratulations! If not, consider revising and submitting it to another journal.
- Address reviewer comments : Reviewers may provide comments and suggestions for revisions to your paper. Address these comments carefully and thoughtfully to improve the quality of your paper.
- Submit the final version: Once your revisions are complete, submit the final version of your paper to the journal. Be sure to follow any additional formatting guidelines and requirements provided by the journal.
- Publication : If your paper is accepted, it will be published in the journal. Some journals provide online publication while others may publish a print version. Be sure to cite your published paper in future research and communicate your findings to the scientific community.
How to Publish a Research Paper for Students
Here are some steps you can follow to publish a research paper as an Under Graduate or a High School Student:
- Select a topic: Choose a topic that is relevant and interesting to you, and that you have a good understanding of.
- Conduct research : Gather information and data on your chosen topic through research, experiments, surveys, or other means.
- Write the paper : Start with an outline, then write the introduction, methods, results, discussion, and conclusion sections of the paper. Be sure to follow any guidelines provided by your instructor or the journal you plan to submit to.
- Edit and revise: Review your paper for errors in spelling, grammar, and punctuation. Ask a peer or mentor to review your paper and provide feedback for improvement.
- Choose a journal : Look for journals that publish papers in your field of study and that are appropriate for your level of research. Some popular journals for students include PLOS ONE, Nature, and Science.
- Submit the paper: Follow the submission guidelines for the journal you choose, which typically include a cover letter, abstract, and formatting requirements. Be prepared to wait several weeks to months for a response.
- Address feedback : If your paper is accepted with revisions, address the feedback from the reviewers and resubmit your paper. If your paper is rejected, review the feedback and consider revising and resubmitting to a different journal.
How to Publish a Research Paper for Free
Publishing a research paper for free can be challenging, but it is possible. Here are some steps you can take to publish your research paper for free:
- Choose a suitable open-access journal: Look for open-access journals that are relevant to your research area. Open-access journals allow readers to access your paper without charge, so your work will be more widely available.
- Check the journal’s reputation : Before submitting your paper, ensure that the journal is reputable by checking its impact factor, publication history, and editorial board.
- Follow the submission guidelines : Every journal has specific guidelines for submitting papers. Make sure to follow these guidelines carefully to increase the chances of acceptance.
- Submit your paper : Once you have completed your research paper, submit it to the journal following their submission guidelines.
- Wait for the review process: Your paper will undergo a peer-review process, where experts in your field will evaluate your work. Be patient during this process, as it can take several weeks or even months.
- Revise your paper : If your paper is rejected, don’t be discouraged. Revise your paper based on the feedback you receive from the reviewers and submit it to another open-access journal.
- Promote your research: Once your paper is published, promote it on social media and other online platforms. This will increase the visibility of your work and help it reach a wider audience.
Journals and Conferences for Free Research Paper publications
Here are the websites of the open-access journals and conferences mentioned:
Open-Access Journals:
- PLOS ONE – https://journals.plos.org/plosone/
- BMC Research Notes – https://bmcresnotes.biomedcentral.com/
- Frontiers in… – https://www.frontiersin.org/
- Journal of Open Research Software – https://openresearchsoftware.metajnl.com/
- PeerJ – https://peerj.com/
Conferences:
- IEEE Global Communications Conference (GLOBECOM) – https://globecom2022.ieee-globecom.org/
- IEEE International Conference on Computer Communications (INFOCOM) – https://infocom2022.ieee-infocom.org/
- IEEE International Conference on Data Mining (ICDM) – https://www.ieee-icdm.org/
- ACM SIGCOMM Conference on Data Communication (SIGCOMM) – https://conferences.sigcomm.org/sigcomm/
- ACM Conference on Computer and Communications Security (CCS) – https://www.sigsac.org/ccs/CCS2022/
Importance of Research Paper Publication
Research paper publication is important for several reasons, both for individual researchers and for the scientific community as a whole. Here are some reasons why:
- Advancing scientific knowledge : Research papers provide a platform for researchers to present their findings and contribute to the body of knowledge in their field. These papers often contain novel ideas, experimental data, and analyses that can help to advance scientific understanding.
- Building a research career : Publishing research papers is an essential component of building a successful research career. Researchers are often evaluated based on the number and quality of their publications, and having a strong publication record can increase one’s chances of securing funding, tenure, or a promotion.
- Peer review and quality control: Publication in a peer-reviewed journal means that the research has been scrutinized by other experts in the field. This peer review process helps to ensure the quality and validity of the research findings.
- Recognition and visibility : Publishing a research paper can bring recognition and visibility to the researchers and their work. It can lead to invitations to speak at conferences, collaborations with other researchers, and media coverage.
- Impact on society : Research papers can have a significant impact on society by informing policy decisions, guiding clinical practice, and advancing technological innovation.
Advantages of Research Paper Publication
There are several advantages to publishing a research paper, including:
- Recognition: Publishing a research paper allows researchers to gain recognition for their work, both within their field and in the academic community as a whole. This can lead to new collaborations, invitations to conferences, and other opportunities to share their research with a wider audience.
- Career advancement : A strong publication record can be an important factor in career advancement, particularly in academia. Publishing research papers can help researchers secure funding, grants, and promotions.
- Dissemination of knowledge : Research papers are an important way to share new findings and ideas with the broader scientific community. By publishing their research, scientists can contribute to the collective body of knowledge in their field and help advance scientific understanding.
- Feedback and peer review : Publishing a research paper allows other experts in the field to provide feedback on the research, which can help improve the quality of the work and identify potential flaws or limitations. Peer review also helps ensure that research is accurate and reliable.
- Citation and impact : Published research papers can be cited by other researchers, which can help increase the impact and visibility of the research. High citation rates can also help establish a researcher’s reputation and credibility within their field.
About the author
Muhammad Hassan
Researcher, Academic Writer, Web developer
You may also like

APA Table of Contents – Format and Example

Research Paper Format – Types, Examples and...

Implications in Research – Types, Examples and...

Research Paper Introduction – Writing Guide and...

How to Cite Research Paper – All Formats and...

Scope of the Research – Writing Guide and...
Thank you for visiting nature.com. You are using a browser version with limited support for CSS. To obtain the best experience, we recommend you use a more up to date browser (or turn off compatibility mode in Internet Explorer). In the meantime, to ensure continued support, we are displaying the site without styles and JavaScript.
- View all journals
How to publish your paper
On this page, journal specific instructions, nature journal pledge to authors, how to publish your research in a nature journal, editorial process, about advance online publication, journals' aop timetable, frequently asked questions.
For more information on how to publish papers in a specific Nature Portfolio title, please visit the author instructions page for the journal that is of interest to you.
Top of page ⤴
Editors of the Nature journals strive to provide authors with an outstandingly efficient, fair and thoughtful submission, peer-review and publishing experience. Authors can expect all manuscripts that are published to be scrutinized for peer-review with the utmost professional rigor and care by expert referees who are selected by the editors for their ability to provide incisive and useful analysis. Editors weigh many factors when choosing content for Nature journals, but they strive to minimize the time taken to make decisions about publication while maintaining the highest possible quality of that decision.
After review, editors work to increase a paper's readability, and thereby its audience, through advice and editing, so that all research is presented in a form that is both readable to those in the field and understandable to scientists outside the immediate discipline. Research is published online without delay through our Advance Online Publication system. Nature journals provide more than 3,000 registered journalists with weekly press releases that mention all research papers to be published. About 800,000 registered users receive e-mailed tables of contents, and many papers are highlighted for the nonspecialist reader on the journal's homepage, contents pages and in News and Views.
Throughout this process, the editors of Nature journals uphold editorial, ethical and scientific standards according to the policies outlined on the author and referee site as well as on our journal websites. We periodically review those policies to ensure that they continue to reflect the needs of the scientific community, and welcome comments and suggestions from scientists, either via the feedback links on the author and referees' website or via our author blog, Nautilus , or peer-review blog, Peer to Peer .
The Nature journals comprise the weekly, multidisciplinary Nature, which publishes research of the highest influence within a discipline that will be of interest to scientists in other fields, and fifteen monthly titles, publishing papers of the highest quality and of exceptional impact: Nature Biotechnology, Nature Cell Biology, Nature Chemical Biology, Nature Chemistry, Nature Climate Change, Nature Communications, Nature Genetics, Nature Geoscience, Nature Immunology, Nature Materials, Nature Medicine, Nature Methods, Nature Nanotechnology, Nature Neuroscience, Nature Photonics, Nature Physics, Nature Protocolsand Nature Structural and Molecular Biology. These journals are international, being published and printed in the United States, the United Kingdom and Japan. See here for more information about the relationship between these journals.
Nature and the Nature monthly journals have Impact Factors that are among the highest in the world. The high prestige of these journals brings many rewards to their authors, but also means that competition for publication is severe, so many submissions have to be declined without peer-review.
The Nature journals differ from most other journals in that they do not have editorial boards, but are instead run by professional editors who consult widely among the scientific community in making decisions about publication of papers. This article is to provide you with an overview of the general editorial processes of these unique journals. Although the journals are broadly similar and share editorial policies , all authors should consult the author information pages of the specific Nature journal before submitting, to obtain detailed information on criteria for publication and manuscript preparation for that journal, as some differences exist.
The following sections summarise the journals' editorial processes and describe how manuscripts are handled by editors between submission and publication. At all stages of the process, you can access the online submission system and find the status of your manuscript.
Presubmission enquiries
Many Nature journals allow researchers to obtain informal feedback from editors before submitting the whole manuscript. This service is intended to save you time — if the editors feel it would not be suitable, you can submit the manuscript to another journal without delay. If you wish to use the presubmission enquiry service, please use the online system of the journal of your choice to send a paragraph explaining the importance of your manuscript, as well as the abstract or summary paragraph with its associated citation list so the editors may judge the manuscript in relation to other related work. The editors will quickly either invite you to submit the whole manuscript (which does not mean any commitment to publication), or will say that it is not suitable for the journal. If you receive a negative response, please do not reply. If you are convinced of the importance of your manuscript despite editors' reservations, you may submit the whole manuscript using the journal's online submission system. The editors can then make a more complete assessment of your work. Note that not all Nature journals offer a presubmission enquiry service.
Initial submission
When you are ready to submit the manuscript, please use the online submission system for the journal concerned. When the journal receives your manuscript, it will be assigned a number and an editor, who reads the manuscript, seeks informal advice from scientific advisors and editorial colleagues, and compares your submission to other recently published papers in the field. If the manuscript seems novel and arresting, and the work described has both immediate and far-reaching implications, the editor will send it out for peer review, usually to two or three independent specialists. However, because the journals can publish only a few of the manuscripts in the field or subfield concerned, many manuscripts have to be declined without peer review even though they may describe solid scientific results.
Transfers between Nature journals
In some cases, an editor is unable to offer publication, but might suggest that the manuscript is more suitable for one of the other Nature journals. If you wish to resubmit your manuscript to the suggested journal, you can simply follow the link provided by the editor to transfer your manuscript and the reviewers' comments to the new journal. This process is entirely in your control: you can choose not to use this service and instead to submit your manuscript to any other Nature or nature research journal, with or without including the reviewers' comments if you wish, using the journal's usual online submission service. For more information, please see the manuscript transfers page .
Peer review
The corresponding author is notified by email when an editor decides to send a manuscript for review. The editors choose referees for their independence, ability to evaluate the technical aspects of the paper fully and fairly, whether they are currently or recently assessing related submissions, and whether they can review the manuscript within the short time requested.
You may suggest referees for your manuscript (including address details), so long as they are independent scientists. These suggestions are often helpful, although they are not always followed. Editors will honour your requests to exclude a limited number of named scientists as reviewers.
Decisions and revisions
If the editor invites you to revise your manuscript, you should include with your resubmitted version a new cover letter that includes a point-by-point response to the reviewers' and editors' comments, including an explanation of how you have altered your manuscript in response to these, and an estimation of the length of the revised version with figures/tables. The decision letter will specify a deadline, and revisions that are returned within this period will retain their original submission date.
Additional supplementary information is published with the online version of your article if the editors and referees have judged that it is essential for the conclusions of the article (for example, a large table of data or the derivation of a model) but of more specialist interest than the rest of the article. Editors encourage authors whose articles describe methods to provide a summary of the method for the print version and to include full details and protocols online. Authors are also encouraged to post the full protocol on Nature Protocols' Protocol Exchange , which as well as a protocols database provides an online forum for readers in the field to add comments, suggestions and refinements to the published protocols.
After acceptance
Your accepted manuscript is prepared for publication by copy editors (also called subeditors), who refine it so that the text and figures are readable and clear to those outside the immediate field; choose keywords to maximize visibility in online searches as well as suitable for indexing services; and ensure that the manuscripts conform to house style. The copy editors are happy to give advice to authors whose native language is not English, and will edit those papers with special care.
After publication
All articles are published in the print edition and, in PDF and HTML format, in the online edition of the journal, in full. Many linking and navigational services are provided with the online (HTML) version of all articles published by the Nature journals.
All articles and contact details of corresponding authors are included in our press release service, which means that your work is drawn to the attention of all the main media organizations in the world, who may choose to feature the work in newspaper and other media reports. Some articles are summarized and highlighted within Nature and Nature Portfolio publications and subject-specific websites.
Journals published by Nature Portfolio do not ask authors for copyright, but instead ask you to sign an exclusive publishing license . This allows you to archive the accepted version of your manuscript six months after publication on your own, your institution's, and your funder's websites.
Disagreements with decisions
If a journal's editors are unable to offer publication of a manuscript and have not invited resubmission, you are strongly advised to submit your manuscript for publication elsewhere. However, if you believe that the editors or reviewers have seriously misunderstood your manuscript, you may write to the editors, explaining the scientific reasons why you believe the decision was incorrect. Please bear in mind that editors prioritise newly submitted manuscripts and manuscripts where resubmission has been invited, so it can take several weeks before letters of disagreement can be answered. During this time, you must not submit your manuscript elsewhere. In the interests of publishing your results without unnecessary delay, we therefore advise you to submit your manuscript to another journal if it has been declined, rather than to spend time on corresponding further with the editors of the declining journal.
Nature journals offer Advance Online Publication (AOP).
We believe that AOP is the best and quickest way to publish high-quality, peer-reviewed research for the benefit of readers and authors. Papers published AOP are the definitive version: they do not change before appearing in print and can be referenced formally as soon as they appear on the journal's AOP website. In addition, Nature publishes some papers each week via an Accelerated Article Preview (AAP) workflow. For these papers, we upload the accepted manuscript to our website as an AAP PDF, without subediting of text, figures or tables, but with some preliminary formatting. AAP papers are clearly indicated by a watermark on each page of the online PDF.
Each journal's website includes an AOP table of contents, in which papers are listed in order of publication date (beginning with the most recent). Each paper carries a digital object identifier (DOI), which serves as a unique electronic identification tag for that paper. As soon as the issue containing the paper is printed, papers will be removed from the AOP table of contents, assigned a page number and transferred to that issue's table of contents on the website. The DOI remains attached to the paper to provide a persistent identifier.
Nature publishes many, but not all, papers AOP, on Mondays and Wednesdays.
For the monthly Nature journals publishing primary research, new articles are uploaded to the AOP section of their web sites once each week. Occasionally, an article may be uploaded on other days.
The monthly Nature Reviews journals also upload new articles to the AOP section of their web sites once each week.
Q. Which articles are published AOP?
A. Original research is published AOP — that is, Articles and Letters, and for the Nature journals that publish them, Brief Communications. Associated News and Views articles may be published with the AOP Article or Letter or when the papers are published in the print/online edition of the journal. Nature occasionally publishes other article types AOP, for example News and Commentaries.
Q. Is the AOP version of the article definitive?
A. Yes. Only the final version of the paper is published AOP, exactly as it will be published in the printed edition. The paper is thus complete in every respect except that instead of having a volume/issue/page number, it has a DOI (digital object identifier). This means that the paper can be referenced as soon as it appears on the AOP site by using the DOI. Nature also publishes some papers each week via an Accelerated Article Preview workflow, where the accepted version of the paper is uploaded as a PDF to our website without subediting of text, figures and tables, but with some preliminary formatting. These papers are clearly identified by a watermark on each page of the PDF.
Q. What is a Digital Object Identifier?
A. The DOI is an international, public, "persistent identifier of intellectual property entities" in the form of a combination of numbers and letters. For Nature Portfolio journals, the DOI is assigned to an item of editorial content, providing a unique and persistent identifier for that item. The DOI system is administered by the International DOI Foundation, a not-for-profit organization. CrossRef, another not-for-profit organization, uses the DOI as a reference linking standard, enables cross-publisher linking, and maintains the lookup system for DOIs. Nature Portfolio is a member of CrossRef.
Q. What do the numbers in the DOI signify?
A. The DOI has two components, a prefix (before the slash) and a suffix (after the slash). The prefix is a DOI resolver server identifer (10) and a unique identifier assigned to the publisher—for example, the identifier for Nature Portfolio is 1038 and the entire DOI prefix for an article published by Nature Portfolio is 10.1038. The suffix is an arbitrary number provided by the publisher. It can be composed of numbers and/or letters and does not necessarily have any systematic significance. Each DOI is registered in a central resolution database that associates it with one or more corresponding web locations (URLs). For example, the DOI 10.1038/ng571 connects to http://dx.doi.org/10.1038/ng571.
Q. Can I use the DOI in a reference citation?
A. Yes, instead of giving the volume and page number, you can give the paper's DOI at the end of the citation. For example, Nature papers should be cited in the form;
Author(s) Nature advance online publication, day month year (DOI 10.1038/natureXXX).
After print publication, you should give the DOI as well as the print citation, to enable readers to find the paper in print as well as online. For example;
Author(s) Nature volume, page (year); advance online publication, day month year (DOI 10.1038/natureXXX).
Q. How can I use a DOI to find a paper?
A. There are two ways:
- DOIs from other articles can be embedded into the linking coding of an article's reference section. In Nature journals these appear as "|Article|" in the reference sections. When |Article| is clicked, it opens another browser window leading to the entrance page (often the abstract) for another article. Depending on the source of the article, this page can be on the Nature Portfolio's site or a site of another publisher. This service is enabled by CrossRef.
- A DOI can be inserted directly into the browser. For example, for the DOI 10.1038/ng571, typing http://dx.doi.org/10.1038/ng571 brings up the entrance page of the article.
Q. What is the official publication date?
A. Many journals, and most abstracting and indexing services (including Medline and Thomson-Reuters) cite the print date as the publication date. Publishers usually state both the 'online publication date' and the 'print publication date'. Nature Portfolio publishes both dates for our own papers, in the hope that scientific communities, as well as abstracting and indexing services, will recognize these dates.
We endeavour to include both the online publication date and the usual print citation in reference lists of Nature Portfolio papers, where a paper has been published online before being published in print. Given the use of the DOI in locating an online publication in the future, we encourage authors to use DOIs in reference citations.
For legal purposes (for example, establishing intellectual property rights), we assume that online publication constitutes public disclosure. But this is for the courts to decide; Nature Portfolio's role as a publisher is to provide clear documentation of the publication history, online and in print.
Q. Must I be a subscriber to read AOP articles?
A. Yes. AOP papers are the same as those in the print/online issues: while abstracts are freely available on any Nature Portfolio journal's web site, access to the full-text article requires a paid subscription or a site license.
Q. Does Medline use DOIs?
A. Medline currently captures DOIs with online publication dates in its records, and is developing an enhanced level of support for the DOI system.
Q. Does Thomson-Reuters use DOIs?
A. Thomson Reuters captures DOIs in its records at the same time as the volume/issue/page number. Therefore, it is not using the DOI to capture information before print publication, but rather as an additional piece of metadata.

Q. How does AOP affect the Impact Factor?
A. Impact factors are calculated by Thomson-Reuters. At present, Thomson-Reuters bases its calculations on the date of print publication alone, so until or unless it changes its policy, AOP has no effect on impact factors.
Q. What are the page numbers in PDFs of AOP papers?
A. For convenience, the PDF version of every AOP article is given a temporary pagination, beginning with page 1. This is unrelated to the final pagination in the printed article.
Quick links
- Explore articles by subject
- Guide to authors
- Editorial policies
An official website of the United States government
The .gov means it’s official. Federal government websites often end in .gov or .mil. Before sharing sensitive information, make sure you’re on a federal government site.
The site is secure. The https:// ensures that you are connecting to the official website and that any information you provide is encrypted and transmitted securely.
- Publications
- Account settings
The PMC website is updating on October 15, 2024. Learn More or Try it out now .
- Advanced Search
- Journal List

How to Write and Publish a Research Paper for a Peer-Reviewed Journal
Clara busse.
1 Department of Maternal and Child Health, University of North Carolina Gillings School of Global Public Health, 135 Dauer Dr, 27599 Chapel Hill, NC USA
Ella August
2 Department of Epidemiology, University of Michigan School of Public Health, 1415 Washington Heights, Ann Arbor, MI 48109-2029 USA
Associated Data
Communicating research findings is an essential step in the research process. Often, peer-reviewed journals are the forum for such communication, yet many researchers are never taught how to write a publishable scientific paper. In this article, we explain the basic structure of a scientific paper and describe the information that should be included in each section. We also identify common pitfalls for each section and recommend strategies to avoid them. Further, we give advice about target journal selection and authorship. In the online resource 1 , we provide an example of a high-quality scientific paper, with annotations identifying the elements we describe in this article.
Electronic supplementary material
The online version of this article (10.1007/s13187-020-01751-z) contains supplementary material, which is available to authorized users.
Introduction
Writing a scientific paper is an important component of the research process, yet researchers often receive little formal training in scientific writing. This is especially true in low-resource settings. In this article, we explain why choosing a target journal is important, give advice about authorship, provide a basic structure for writing each section of a scientific paper, and describe common pitfalls and recommendations for each section. In the online resource 1 , we also include an annotated journal article that identifies the key elements and writing approaches that we detail here. Before you begin your research, make sure you have ethical clearance from all relevant ethical review boards.
Select a Target Journal Early in the Writing Process
We recommend that you select a “target journal” early in the writing process; a “target journal” is the journal to which you plan to submit your paper. Each journal has a set of core readers and you should tailor your writing to this readership. For example, if you plan to submit a manuscript about vaping during pregnancy to a pregnancy-focused journal, you will need to explain what vaping is because readers of this journal may not have a background in this topic. However, if you were to submit that same article to a tobacco journal, you would not need to provide as much background information about vaping.
Information about a journal’s core readership can be found on its website, usually in a section called “About this journal” or something similar. For example, the Journal of Cancer Education presents such information on the “Aims and Scope” page of its website, which can be found here: https://www.springer.com/journal/13187/aims-and-scope .
Peer reviewer guidelines from your target journal are an additional resource that can help you tailor your writing to the journal and provide additional advice about crafting an effective article [ 1 ]. These are not always available, but it is worth a quick web search to find out.
Identify Author Roles Early in the Process
Early in the writing process, identify authors, determine the order of authors, and discuss the responsibilities of each author. Standard author responsibilities have been identified by The International Committee of Medical Journal Editors (ICMJE) [ 2 ]. To set clear expectations about each team member’s responsibilities and prevent errors in communication, we also suggest outlining more detailed roles, such as who will draft each section of the manuscript, write the abstract, submit the paper electronically, serve as corresponding author, and write the cover letter. It is best to formalize this agreement in writing after discussing it, circulating the document to the author team for approval. We suggest creating a title page on which all authors are listed in the agreed-upon order. It may be necessary to adjust authorship roles and order during the development of the paper. If a new author order is agreed upon, be sure to update the title page in the manuscript draft.
In the case where multiple papers will result from a single study, authors should discuss who will author each paper. Additionally, authors should agree on a deadline for each paper and the lead author should take responsibility for producing an initial draft by this deadline.
Structure of the Introduction Section
The introduction section should be approximately three to five paragraphs in length. Look at examples from your target journal to decide the appropriate length. This section should include the elements shown in Fig. 1 . Begin with a general context, narrowing to the specific focus of the paper. Include five main elements: why your research is important, what is already known about the topic, the “gap” or what is not yet known about the topic, why it is important to learn the new information that your research adds, and the specific research aim(s) that your paper addresses. Your research aim should address the gap you identified. Be sure to add enough background information to enable readers to understand your study. Table Table1 1 provides common introduction section pitfalls and recommendations for addressing them.

The main elements of the introduction section of an original research article. Often, the elements overlap
Common introduction section pitfalls and recommendations
| Pitfall | Recommendation |
|---|---|
| Introduction is too generic, not written to specific readers of a designated journal. | Visit your target journal’s website and investigate the journal’s readership. If you are writing for a journal with a more general readership, like PLOS ONE, you should include more background information. A narrower journal, like the Journal of the American Mosquito Control Association, may require less background information because most of its readers have expertise in the subject matter. |
| Citations are inadequate to support claims. | If a claim could be debated, it should be supported by one or more citations. To find articles relevant to your research, consider using open-access journals, which are available for anyone to read for free. A list of open-access journals can be found here: . You can also find open-access articles using PubMed Central: |
| The research aim is vague. | Be sure that your research aim contains essential details like the setting, population/sample, study design, timing, dependent variable, and independent variables. Using such details, the reader should be able to imagine the analysis you have conducted. |
Methods Section
The purpose of the methods section is twofold: to explain how the study was done in enough detail to enable its replication and to provide enough contextual detail to enable readers to understand and interpret the results. In general, the essential elements of a methods section are the following: a description of the setting and participants, the study design and timing, the recruitment and sampling, the data collection process, the dataset, the dependent and independent variables, the covariates, the analytic approach for each research objective, and the ethical approval. The hallmark of an exemplary methods section is the justification of why each method was used. Table Table2 2 provides common methods section pitfalls and recommendations for addressing them.
Common methods section pitfalls and recommendations
| Pitfall | Recommendation |
|---|---|
| The author only describes methods for one study aim, or part of an aim. |
Be sure to check that the methods describe all aspects of the study reported in the manuscript. |
| There is not enough (or any) justification for the methods used. | You must justify your choice of methods because it greatly impacts the interpretation of results. State the methods you used and then defend those decisions. For example, justify why you chose to include the measurements, covariates, and statistical approaches. |
Results Section
The focus of the results section should be associations, or lack thereof, rather than statistical tests. Two considerations should guide your writing here. First, the results should present answers to each part of the research aim. Second, return to the methods section to ensure that the analysis and variables for each result have been explained.
Begin the results section by describing the number of participants in the final sample and details such as the number who were approached to participate, the proportion who were eligible and who enrolled, and the number of participants who dropped out. The next part of the results should describe the participant characteristics. After that, you may organize your results by the aim or by putting the most exciting results first. Do not forget to report your non-significant associations. These are still findings.
Tables and figures capture the reader’s attention and efficiently communicate your main findings [ 3 ]. Each table and figure should have a clear message and should complement, rather than repeat, the text. Tables and figures should communicate all salient details necessary for a reader to understand the findings without consulting the text. Include information on comparisons and tests, as well as information about the sample and timing of the study in the title, legend, or in a footnote. Note that figures are often more visually interesting than tables, so if it is feasible to make a figure, make a figure. To avoid confusing the reader, either avoid abbreviations in tables and figures, or define them in a footnote. Note that there should not be citations in the results section and you should not interpret results here. Table Table3 3 provides common results section pitfalls and recommendations for addressing them.
Common results section pitfalls and recommendations
| Pitfall | Recommendation |
|---|---|
| The text focuses on statistical tests rather than associations. | The relationships between independent and dependent variables are at the heart of scientific studies and statistical tests are a set of strategies used to elucidate such relationships. For example, instead of reporting that “the odds ratio is 3.4,” report that “women with exposure X were 3.4 times more likely to have disease Y.” There are several ways to express such associations, but all successful approaches focus on the relationships between the variables. |
| Causal words like “cause” and “impact” are used inappropriately | Only some study designs and analytic approaches enable researchers to make causal claims. Before you use the word “cause,” consider whether this is justified given your design. Words like “associated” or “related” may be more appropriate. |
| The direction of association unclear. |
Instead of “X is associated with Y,” say “an increase in variable X is associated with a decrease in variable Y,” a sentence which more fully describes the relationship between the two variables. |
Discussion Section
Opposite the introduction section, the discussion should take the form of a right-side-up triangle beginning with interpretation of your results and moving to general implications (Fig. 2 ). This section typically begins with a restatement of the main findings, which can usually be accomplished with a few carefully-crafted sentences.

Major elements of the discussion section of an original research article. Often, the elements overlap
Next, interpret the meaning or explain the significance of your results, lifting the reader’s gaze from the study’s specific findings to more general applications. Then, compare these study findings with other research. Are these findings in agreement or disagreement with those from other studies? Does this study impart additional nuance to well-accepted theories? Situate your findings within the broader context of scientific literature, then explain the pathways or mechanisms that might give rise to, or explain, the results.
Journals vary in their approach to strengths and limitations sections: some are embedded paragraphs within the discussion section, while some mandate separate section headings. Keep in mind that every study has strengths and limitations. Candidly reporting yours helps readers to correctly interpret your research findings.
The next element of the discussion is a summary of the potential impacts and applications of the research. Should these results be used to optimally design an intervention? Does the work have implications for clinical protocols or public policy? These considerations will help the reader to further grasp the possible impacts of the presented work.
Finally, the discussion should conclude with specific suggestions for future work. Here, you have an opportunity to illuminate specific gaps in the literature that compel further study. Avoid the phrase “future research is necessary” because the recommendation is too general to be helpful to readers. Instead, provide substantive and specific recommendations for future studies. Table Table4 4 provides common discussion section pitfalls and recommendations for addressing them.
Common discussion section pitfalls and recommendations
| Pitfall | Recommendation |
|---|---|
| The author repeats detailed results or presents new results in the discussion section. | Recall from Fig. that the discussion section should take the shape of a triangle as it moves from a specific restatement of the main findings to a broader discussion of the scientific literature and implications of the study. Specific values should not be repeated in the discussion. It is also not appropriate to include new results in the discussion section. |
| The author fails to describe the implication of the study’s limitations. | No matter how well-conducted and thoughtful, all studies have limitations. Candidly describe how the limitations affect the application of the findings. |
| Statements about future research are too generic. | Is the relationship between exposure and outcome not well-described in a population that is severely impacted? Or might there be another variable that modifies the relationship between exposure and outcome? This is your opportunity to suggest areas requiring further study in your field, steering scientific inquiry toward the most meaningful questions. |
Follow the Journal’s Author Guidelines
After you select a target journal, identify the journal’s author guidelines to guide the formatting of your manuscript and references. Author guidelines will often (but not always) include instructions for titles, cover letters, and other components of a manuscript submission. Read the guidelines carefully. If you do not follow the guidelines, your article will be sent back to you.
Finally, do not submit your paper to more than one journal at a time. Even if this is not explicitly stated in the author guidelines of your target journal, it is considered inappropriate and unprofessional.
Your title should invite readers to continue reading beyond the first page [ 4 , 5 ]. It should be informative and interesting. Consider describing the independent and dependent variables, the population and setting, the study design, the timing, and even the main result in your title. Because the focus of the paper can change as you write and revise, we recommend you wait until you have finished writing your paper before composing the title.
Be sure that the title is useful for potential readers searching for your topic. The keywords you select should complement those in your title to maximize the likelihood that a researcher will find your paper through a database search. Avoid using abbreviations in your title unless they are very well known, such as SNP, because it is more likely that someone will use a complete word rather than an abbreviation as a search term to help readers find your paper.
After you have written a complete draft, use the checklist (Fig. (Fig.3) 3 ) below to guide your revisions and editing. Additional resources are available on writing the abstract and citing references [ 5 ]. When you feel that your work is ready, ask a trusted colleague or two to read the work and provide informal feedback. The box below provides a checklist that summarizes the key points offered in this article.

Checklist for manuscript quality
(PDF 362 kb)
Acknowledgments
Ella August is grateful to the Sustainable Sciences Institute for mentoring her in training researchers on writing and publishing their research.
Code Availability
Not applicable.
Data Availability
Compliance with ethical standards.
The authors declare that they have no conflict of interest.
Publisher’s Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
- PRO Courses Guides New Tech Help Pro Expert Videos About wikiHow Pro Upgrade Sign In
- EDIT Edit this Article
- EXPLORE Tech Help Pro About Us Random Article Quizzes Request a New Article Community Dashboard This Or That Game Happiness Hub Popular Categories Arts and Entertainment Artwork Books Movies Computers and Electronics Computers Phone Skills Technology Hacks Health Men's Health Mental Health Women's Health Relationships Dating Love Relationship Issues Hobbies and Crafts Crafts Drawing Games Education & Communication Communication Skills Personal Development Studying Personal Care and Style Fashion Hair Care Personal Hygiene Youth Personal Care School Stuff Dating All Categories Arts and Entertainment Finance and Business Home and Garden Relationship Quizzes Cars & Other Vehicles Food and Entertaining Personal Care and Style Sports and Fitness Computers and Electronics Health Pets and Animals Travel Education & Communication Hobbies and Crafts Philosophy and Religion Work World Family Life Holidays and Traditions Relationships Youth
- Browse Articles
- Learn Something New
- Quizzes Hot
- Happiness Hub
- This Or That Game
- Train Your Brain
- Explore More
- Support wikiHow
- About wikiHow
- Log in / Sign up
- Education and Communications
- College University and Postgraduate
- Academic Writing
- Research Papers
How to Write and Publish Your Research in a Journal
Last Updated: May 26, 2024 Fact Checked
Choosing a Journal
Writing the research paper, editing & revising your paper, submitting your paper, navigating the peer review process, research paper help.
This article was co-authored by Matthew Snipp, PhD and by wikiHow staff writer, Cheyenne Main . C. Matthew Snipp is the Burnet C. and Mildred Finley Wohlford Professor of Humanities and Sciences in the Department of Sociology at Stanford University. He is also the Director for the Institute for Research in the Social Science’s Secure Data Center. He has been a Research Fellow at the U.S. Bureau of the Census and a Fellow at the Center for Advanced Study in the Behavioral Sciences. He has published 3 books and over 70 articles and book chapters on demography, economic development, poverty and unemployment. He is also currently serving on the National Institute of Child Health and Development’s Population Science Subcommittee. He holds a Ph.D. in Sociology from the University of Wisconsin—Madison. There are 13 references cited in this article, which can be found at the bottom of the page. This article has been fact-checked, ensuring the accuracy of any cited facts and confirming the authority of its sources. This article has been viewed 707,484 times.
Publishing a research paper in a peer-reviewed journal allows you to network with other scholars, get your name and work into circulation, and further refine your ideas and research. Before submitting your paper, make sure it reflects all the work you’ve done and have several people read over it and make comments. Keep reading to learn how you can choose a journal, prepare your work for publication, submit it, and revise it after you get a response back.
Things You Should Know
- Create a list of journals you’d like to publish your work in and choose one that best aligns with your topic and your desired audience.
- Prepare your manuscript using the journal’s requirements and ask at least 2 professors or supervisors to review your paper.
- Write a cover letter that “sells” your manuscript, says how your research adds to your field and explains why you chose the specific journal you’re submitting to.

- Ask your professors or supervisors for well-respected journals that they’ve had good experiences publishing with and that they read regularly.
- Many journals also only accept specific formats, so by choosing a journal before you start, you can write your article to their specifications and increase your chances of being accepted.
- If you’ve already written a paper you’d like to publish, consider whether your research directly relates to a hot topic or area of research in the journals you’re looking into.

- Review the journal’s peer review policies and submission process to see if you’re comfortable creating or adjusting your work according to their standards.
- Open-access journals can increase your readership because anyone can access them.

- Scientific research papers: Instead of a “thesis,” you might write a “research objective” instead. This is where you state the purpose of your research.
- “This paper explores how George Washington’s experiences as a young officer may have shaped his views during difficult circumstances as a commanding officer.”
- “This paper contends that George Washington’s experiences as a young officer on the 1750s Pennsylvania frontier directly impacted his relationship with his Continental Army troops during the harsh winter at Valley Forge.”

- Scientific research papers: Include a “materials and methods” section with the step-by-step process you followed and the materials you used. [5] X Research source
- Read other research papers in your field to see how they’re written. Their format, writing style, subject matter, and vocabulary can help guide your own paper. [6] X Research source

- If you’re writing about George Washington’s experiences as a young officer, you might emphasize how this research changes our perspective of the first president of the U.S.
- Link this section to your thesis or research objective.
- If you’re writing a paper about ADHD, you might discuss other applications for your research.

- Scientific research papers: You might include your research and/or analytical methods, your main findings or results, and the significance or implications of your research.
- Try to get as many people as you can to read over your abstract and provide feedback before you submit your paper to a journal.

- They might also provide templates to help you structure your manuscript according to their specific guidelines. [11] X Research source

- Not all journal reviewers will be experts on your specific topic, so a non-expert “outsider’s perspective” can be valuable.

- If you have a paper on the purification of wastewater with fungi, you might use both the words “fungi” and “mushrooms.”
- Use software like iThenticate, Turnitin, or PlagScan to check for similarities between the submitted article and published material available online. [15] X Research source

- Header: Address the editor who will be reviewing your manuscript by their name, include the date of submission, and the journal you are submitting to.
- First paragraph: Include the title of your manuscript, the type of paper it is (like review, research, or case study), and the research question you wanted to answer and why.
- Second paragraph: Explain what was done in your research, your main findings, and why they are significant to your field.
- Third paragraph: Explain why the journal’s readers would be interested in your work and why your results are important to your field.
- Conclusion: State the author(s) and any journal requirements that your work complies with (like ethical standards”).
- “We confirm that this manuscript has not been published elsewhere and is not under consideration by another journal.”
- “All authors have approved the manuscript and agree with its submission to [insert the name of the target journal].”

- Submit your article to only one journal at a time.
- When submitting online, use your university email account. This connects you with a scholarly institution, which can add credibility to your work.

- Accept: Only minor adjustments are needed, based on the provided feedback by the reviewers. A first submission will rarely be accepted without any changes needed.
- Revise and Resubmit: Changes are needed before publication can be considered, but the journal is still very interested in your work.
- Reject and Resubmit: Extensive revisions are needed. Your work may not be acceptable for this journal, but they might also accept it if significant changes are made.
- Reject: The paper isn’t and won’t be suitable for this publication, but that doesn’t mean it might not work for another journal.

- Try organizing the reviewer comments by how easy it is to address them. That way, you can break your revisions down into more manageable parts.
- If you disagree with a comment made by a reviewer, try to provide an evidence-based explanation when you resubmit your paper.

- If you’re resubmitting your paper to the same journal, include a point-by-point response paper that talks about how you addressed all of the reviewers’ comments in your revision. [22] X Research source
- If you’re not sure which journal to submit to next, you might be able to ask the journal editor which publications they recommend.

Expert Q&A
You might also like.

- If reviewers suspect that your submitted manuscript plagiarizes another work, they may refer to a Committee on Publication Ethics (COPE) flowchart to see how to move forward. [23] X Research source Thanks Helpful 0 Not Helpful 0

- ↑ https://www.wiley.com/en-us/network/publishing/research-publishing/choosing-a-journal/6-steps-to-choosing-the-right-journal-for-your-research-infographic
- ↑ https://link.springer.com/article/10.1007/s13187-020-01751-z
- ↑ https://libguides.unomaha.edu/c.php?g=100510&p=651627
- ↑ https://www.canberra.edu.au/library/start-your-research/research_help/publishing-research
- ↑ https://writingcenter.fas.harvard.edu/conclusions
- ↑ https://writing.wisc.edu/handbook/assignments/writing-an-abstract-for-your-research-paper/
- ↑ https://www.springer.com/gp/authors-editors/book-authors-editors/your-publication-journey/manuscript-preparation
- ↑ https://apus.libanswers.com/writing/faq/2391
- ↑ https://academicguides.waldenu.edu/library/keyword/search-strategy
- ↑ https://ifis.libguides.com/journal-publishing-guide/submitting-your-paper
- ↑ https://www.springer.com/kr/authors-editors/authorandreviewertutorials/submitting-to-a-journal-and-peer-review/cover-letters/10285574
- ↑ https://www.apa.org/monitor/sep02/publish.aspx
- ↑ Matthew Snipp, PhD. Research Fellow, U.S. Bureau of the Census. Expert Interview. 26 March 2020.
About This Article

To publish a research paper, ask a colleague or professor to review your paper and give you feedback. Once you've revised your work, familiarize yourself with different academic journals so that you can choose the publication that best suits your paper. Make sure to look at the "Author's Guide" so you can format your paper according to the guidelines for that publication. Then, submit your paper and don't get discouraged if it is not accepted right away. You may need to revise your paper and try again. To learn about the different responses you might get from journals, see our reviewer's explanation below. Did this summary help you? Yes No
- Send fan mail to authors
Reader Success Stories
RAMDEV GOHIL
Oct 16, 2017
Did this article help you?
David Okandeji
Oct 23, 2019
Revati Joshi
Feb 13, 2017
Shahzad Khan
Jul 1, 2017
Apr 7, 2017

Featured Articles

Trending Articles

Watch Articles

- Terms of Use
- Privacy Policy
- Do Not Sell or Share My Info
- Not Selling Info
Get all the best how-tos!
Sign up for wikiHow's weekly email newsletter
- How it works

How To Publish A Research Paper? | A Step-By-Step Guide
Published by Alvin Nicolas at September 23rd, 2024 , Revised On September 23, 2024
The process of publishing a research paper can be confusing to many students or first-time authors. It requires careful planning, attention to detail, using academic sources and submitting your manuscript through the submission system.
After writing a research paper comes the most significant step of all. Yes, of course, we are talking about getting it published in a journal. This blog provides you with a step-by-step guide on how to publish your research paper and share it with academic professionals all over the world.
What Is A Research Paper?
A research paper is a piece of academic writing that presents your interpretation, evaluation and findings on a specific topic. It involves extensive research data collection through qualitative and quantitative methods to validate your hypothesis .
A research paper is not easy to write, as it involves understanding the research paper format and guidelines of many journals. It typically consists of an abstract, introduction, literature review, methodologies, results and discussion. But it doesn’t end here, as you need to publish it in well-known journals to create an impact on your work worldwide.
Advantages Of Publishing A Research Paper
Before we dive into the process of publishing a research paper, let’s understand the advantages and benefits of publishing a research paper.
| Your research work can help you get academic recognition and appreciation and advance your career. | |
| Your research work can create an impact and advance knowledge in academic fields. | |
| Publishing a research paper as an undergraduate or as a first-time author can help you get academic funding and credit. It also improves your academic record. | |
| Your research work will provide you with a sense of satisfaction and accomplishment. | |
| When experts check your work for accuracy and transparency, you will get to learn more from your peers. |
Criteria For Publishing A Research Paper
A well-crafted research paper proves to be a valuable resource in academic fields. However, it should meet specific criteria to be eligible for publishing in journals. These criteria can vary from journal to journal, however, here are some common requirements to publish a research paper:
Originality
The research paper should be original and should not have been published anywhere else or previously in some other journal. Also, it should provide advanced knowledge on the chosen topic. The figures included in the manuscript should not be published anywhere else.
High-Technical Standards
Any research methodology or reagent used in the research should be mentioned in a comprehensive manner. The experiment must be carried out properly, with the sample size large enough for robust results. Moreover, the data presented must support the conclusions drawn.
Scientific Merit
The manuscript must be clear and concise for peers and other academic researchers to understand. The research must be ethical and of the highest standards with clear objectives. All ethical considerations should be taken into review such as transparency, accuracy, data privacy, participant’s consent and animal welfare in the case of experiments.
Relevance To Journal
The research paper must be relevant to the journal approached for publishing, and it must focus on the key areas of it. Every journal has its publication criteria, ethical considerations, figure assessment and more, which should all be taken into account.
Standard English
Authors should avoid using unambiguous words that are difficult to understand. Each journal urges that the research work be in standard English. In case of any problem, authors can seek scientific editing services or manuscript editing services online for ease.
Hire an Expert Writer
Orders completed by our expert writers are
- Formally drafted in an academic style
- Free Amendments and 100% Plagiarism Free – or your money back!
- 100% Confidential and Timely Delivery!
- Free anti-plagiarism report
- Appreciated by thousands of clients. Check client reviews
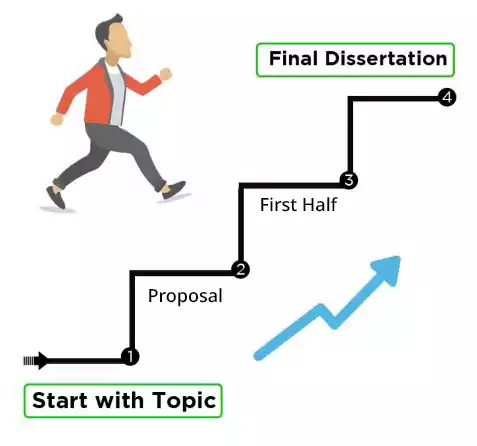
Steps In Publishing A Research Paper
Publishing a research paper involves a great deal of steps. Here is the process of publishing a research paper:
Step 1: Choose A Journal
The first step in getting your paper published is choosing the right journal. The best way to identify the best journal for your paper is by looking at the reference section of your manuscript. Journals only publish manuscripts of topics they have previously published.
Moreover, the tone, format and writing style must be similar to that of articles and papers published by the journal. Another way to find the right journal is by using a journal finder. This helps specify journals related to your work and also mentions journal rankings. For a better understanding, the following questions must be taken into view while selecting a journal for your paper:
- What is my target audience?
- Which journal fits my manuscript?
- Which journals are ranked better and have a higher impact?
- Which journals are open access and which are subscription-based?
- What is the publishing fee for journals?
Some well-known online journals in academic fields are:
- ResearchGate
- Chemical Reviews
- Nature Medicine
- World Psychiatry
Step 2: Prepare Your Paper
After selecting a journal, you should prepare your paper for submission. The tone, structure and format must be according to the journal you chose. Certain journals have a particular format for how tables, figures, and other materials are presented. You should always keep in mind your target journal, and your audience, and use keywords accordingly. Lastly, it is necessary to be aware of the editorial policies of the journal, to avoid any complications in future.
Step 3: Editing And Revising
Before submitting your paper, it is wise to revise it and correct any factual errors and knowledge gaps that might have occurred.
Step 4: Submit Your Paper
After completing the above steps, submit your paper to the journal. Each journal will have specific journal requirements that should be followed. There is no set time when you can expect to hear from the editor. However, a desk rejection may occur if the editor rejects your paper or sends it back for revision and resubmission.
Step 5: The Peer-Review Process
A peer review is an independent assessment of your work by experts in your field. A few research papers get immediate acceptance from peer-reviewed journals. However, rejection is not something to be scared of. It simply means that the journal requires changes before the publication can be considered. Often you will be asked to revise your paper and resubmit it for further feedback. You can also track your paper by the reference number given to you by the journal.
Step 6: The Production Process
When your paper is accepted for publication, it heads into production. Then it is prepared for publishing in the journal that has accepted your research work.
Step 7: Share And Promote
When your research paper is successfully published, access your article on its impact. Sharing research and making notable achievements can get you recognition in the field.
Frequently Asked Questions
How to publish a research paper in an international journal.
To publish a research paper in an international journal, it is necessary to research international journals that specialise in your field. Your paper should adhere to all international standards. Meeting international researchers and developing connections can also be a plus point. Hence, you can submit a cover letter that highlights your work and its need to be published internationally .
What is the average time to publish a research paper?
The process of publication can vary from journal to journal. It can take a few months to over a year.
How to publish a legal research paper?
To submit your legal research paper, you need to choose a solid legal topic. Write a well-structured paper on it, citing any sources and mentioning all references. Lastly, submit it to legal journals that align with your work.
You May Also Like
Is the deadline for your dissertation coming and you haven’t started it yet? Follow our guide on how to write a dissertation in ten days.
This blog gives a breakdown of how much a dissertation costs. An insight into both if you write it yourself or get help from expert services.
Have you been looking to achieve a higher grade, but failed? Learn how essay writing services can help you score better grades this semester…
USEFUL LINKS
LEARNING RESOURCES

COMPANY DETAILS
- How It Works

Making your Research easy
How to publish a paper in International Journal
Publishing a paper in the International Journal is a very important part of every research. In this article, we will discuss the step-by-step process of How to publish a paper in international journal. This will guide you to publish your paper in a good journal successfully.
How to publish a paper in International Journal?
Many of you may have published your research papers in different International Journals.
If you have already done, this then also you may continue reading this article till the end to discover more and the right way to publish the paper in an International Journal. But before that let’s understand.
What is a research journal?
A research journal is a periodical publication in which research relating to a particular academic discipline is published.
Academic journals serve as permanent and transparent forums for the presentation, scrutiny, and discussion of research. International journals are the best place to showcase your research finding and ideas to the world.
Thousands of Journals exist that publish good papers in their regular issues and their journal impact factor is also high.
Now let us understand how to publish a research paper in international journal in easy steps.
Prepare and write your research paper.
Before writing any research paper you must collect all the information about the topic and your research work.
Make some points of your findings and note them down. Choose the journal in which you want to publish the paper. Check the sample paper and “Instruction to Authors” or “Author’s Guide” of that particular journal.
Prepare your manuscript according to the format. Every journal article follows a specific format, such as Abstract, Introduction, Methods, Results, Discussion, Conclusion, and Acknowledgements/References. Future scope and limitations can also be included in your paper.
Also read: How to Publish a Research Paper
Submit your manuscript.
All journals have a specific method of submission of papers like Online submission , Email Submission, and hardcopy submission .
But most of the journals are now accepting only online and email submissions .
If you are asked to submit your paper online then you may need to fill in some other information as well like Name, Affiliation, Contact number, Email ID, Institution’s name, Degree completed or perusing, Years of experience, etc.
Make sure you have given the correct information about yours. Make use of your organizational email ID along with your personal email ID.
Wait for the notification and don’t Panic.
Many authors get panic after submitting the paper and continuously ask for a notification and review report.
But, you need not panic because the Editor may receive several papers for the journal so it takes some time.
Also Read: How To Promote Your Research Article
The initial information you could receive like any of the following statuses
- Accepted: It means your paper has been accepted
- Accepted with Modification: It requires some modification and then it will be accepted.
- Revise and resubmit: It means your paper needed much modification so you can modify it according to the reviewer’s comment.
- Rejected: It means the paper is not suitable for the journal but it does not mean that the paper is not suitable for other journals.
Also read: Top 12 reasons why Journal rejects manuscripts
So take the action accordingly and get your paper published.
If you are looking to publish a research paper then you may search the Green open access journals which do not charge any publication fee from the authors. The Open access journal mostly charges the Article processing charge.
Must read: How much does it cost to publish a paper in a journal
Final words
Journal Publication is a difficult task but if you understand the process and follow the procedure it could be very easy to publish your paper in a good journal. So now, we hope you have understood How to publish a paper in International Journal.

Related Posts
How to convert a Ph.D. thesis into a journal article
What is peer review? All things you need to know
5 Best tips for choosing the right Journal
Redirect Notice
Small research grants (r03).
To provide research support specifically limited in time and amount for studies in categorical program areas. Small grants provide flexibility for initiating studies which are generally for preliminary short-term projects and are non-renewable.
The R03 grant mechanism supports small research projects that can be carried out in a short period of time with limited resources.
Award Information
- Funding Instrument: Grant
- Funding Category: Research and Development
- Budget Mechanism Code: RP - Research Projects
Application and Submission Information
Parent announcements.
R03 Parent Announcement s are available.
Parent announcements are broad funding opportunities that applicants can use to submit investigator-initiated applications for a range of popular programs. They do not specify any particular area of scientific interest. They simply provide the standard forms and instructions needed to apply.
Not all NIH institutes and centers participate on all parent announcements. Check the participating organization in the funding opportunity before applying.
Application Characteristics
- Project period of up to two years (check funding opportunity for exceptions)
- Budget for direct costs of up $50,000 per year (check funding opportunity for exceptions)
- Cannot be renewed
- No preliminary data are required but may be included if available
- Research Strategy may not exceed 6 pages
The common characteristic of the small grant is the provision of limited funding for a short period of time. Examples of the types of projects that ICs support with the R03 include the following:
- Pilot or feasibility studies
- Secondary analysis of existing data
- Small, self-contained research projects
- Development of research methodology
- Development of new research technology
A doctoral student may not apply for an R03 grant to support thesis or dissertation research. An R03 award may be used to assist students who are pursuing dissertation studies when the work is within the scope of the R03 award.
Investigators are strongly encouraged to consult with NIH Scientific/Research staff (see Section VII. Agency Contacts of the funding opportunity) during the concept development stage of the application to determine if an R03 application is appropriate.
After identifying a funding opportunity, follow guidance in the How to Apply – Application Guide including any Research (R) instruction call-outs, except where instructed to do otherwise in the funding opportunity or related notices.
The Key Dates section of funding opportunities lists specific due dates. Many opportunities indicate Standard Due Dates apply.
| Standard Application Due Dates (when applicable) | Review and Award Cycles | ||||
| New | Renewal, Resubmission, Revision as Allowed | AIDS and AIDS Related Grant Applications | Scientific Merit Review | Advisory Council Review | Earliest Start Date |
Participating Funding Organizations
Each funding opportunity specifies the participating organizations. Applications must fit within the mission of at least one participating funding organization and meet all opportunity-specific requirements.
- Division of Program Coordination, Planning and Strategic Initiatives, Office of Disease Prevention ( ODP )
- Eunice Kennedy Shriver National Institute of Child Health and Human Development ( NICHD )
- Fogarty International Center ( FIC )
- National Cancer Institute ( NCI )
- National Center for Complementary and Integrative Health ( NCCIH )
- National Eye Institute ( NEI )
- National Heart, Lung, and Blood Institute ( NHLBI )
- National Human Genome Research Institute ( NHGRI )
- National Institute of Allergy and Infectious Diseases ( NIAID )
- National Institute of Arthritis and Musculoskeletal and Skin Diseases ( NIAMS )
- National Institute of Biomedical Imaging and Bioengineering ( NIBIB )
- National Institute of Dental and Craniofacial Research ( NIDCR )
- National Institute of Diabetes and Digestive and Kidney Diseases ( NIDDK )
- National Institute of Environmental Health Sciences ( NIEHS )
- National Institute of Mental Health ( NIMH )
- National Institute of Neurological Disorders and Stroke ( NINDS )
- National Institute on Aging ( NIA )
- National Institute on Alcohol Abuse and Alcoholism ( NIAAA )
- National Institute on Deafness and Other Communication Disorders ( NIDCD )
- National Institute on Drug Abuse ( NIDA )
- National Institute on Minority Health and Health Disparities ( NIMHD )
- National Library of Medicine ( NLM )
- Office of Behavioral and Social Sciences Research ( OBSSR )
- Office of Research on Women's Health ( ORWH )
- Your organization's sponsored programs office or grants administrators can answer many internal and agency policy and process questions.
- Before you apply, check your chosen funding opportunity for application submission, scientific/research, peer review, and financial/grants management contacts.
- After you apply, find NIH staff assignments in the Status module of eRA Commons .
Security and Privacy Protection of Internet of Things Devices in 6G Networks
- ORIGINAL ARTICLE
- Published: 24 September 2024
Cite this article

- Hailin Liu ORCID: orcid.org/0009-0007-2911-7658 1 ,
- Yuanyuan Wang 1 &
- Fengqi Jia 1
With the gradual maturity of 6G (sixth-generation mobile communication network) technology, the security and privacy protection of Internet of Things (IoT) devices have become the research focus areas. This paper discusses how to improve the security and privacy protection level of IoT devices in a 6G network environment to deal with the low success rate of device authentication, inaccurate detection of malicious behavior, poor vulnerability detection and repair, and weak anti-attack capabilities. In this study, a security architecture for IoT smart devices for 6G networks is first designed; then, a full-dimensional dynamic convolutional network (FDCN) is introduced to learn the IQ (in-phase and quadrature) signal characteristics of the device and complete the device authentication; then, malicious programs are detected through feature differences to achieve security monitoring; finally, a set of vulnerability repair processes is designed. Through experimental verification, the method proposed in this paper has a device authentication success rate of 92% to 100% when the number of authentication attempts is 10 to 50; when the sample size is 100 to 5000, the malicious behavior detection accuracy rate remains between 88 and 95%; in addition, the vulnerability detection time and anti-attack ability have also been significantly improved. Compared with existing methods such as blockchain, edge computing, and joint learning, this method reduces the vulnerability detection time by 12.62 s, 15.08 s, and 13.43 s, respectively; when the attack complexity is 10, the attack resistance reaches 93.59%, which is much higher than other methods.
This is a preview of subscription content, log in via an institution to check access.
Access this article
Subscribe and save.
- Get 10 units per month
- Download Article/Chapter or eBook
- 1 Unit = 1 Article or 1 Chapter
- Cancel anytime
Price includes VAT (Russian Federation)
Instant access to the full article PDF.
Rent this article via DeepDyve
Institutional subscriptions

Explore related subjects
- Artificial Intelligence
Abdur Rahman Md, Shamim Hossain M (2022) A deep learning assisted software-defined security architecture for 6G wireless networks: IIoT perspective. IEEE Wireless Commun 29(2):52–59. https://doi.org/10.1109/MWC.006.2100438
Article Google Scholar
Alzubi Jafar A (2020) Hashed Needham Schroeder industrial IoT based cost optimized deep secured data transmission in the cloud. Measurement 150:107077. https://doi.org/10.1016/j.measurement.2019.107077
Alzubi Omar A, Alzubi Jafar A, Shankar K, Gupta Deepak (2021) Blockchain and artificial intelligence-enabled privacy-preserving medical data transmission in Internet of things. Transa Emerging Telecommun Technolo 32(12):e4360. https://doi.org/10.1002/ett.4360
Alzubi Jafar A, Alzubi Omar A, Singh Ashish, Ramachandran Manikandan (2022) Cloud-IIoT-based electronic health record privacy-preserving by CNN and blockchain-enabled federated learning. IEEE Transa Ind Inf 19(1):1080–1087. https://doi.org/10.1109/TII.2022.3189170
Aman Muhammad Naveed, Javaid Uzair, Sikdar Biplab (2021) Security function virtualization for IoT applications in 6G networks. IEEE Communi Stand Mag 5(3):90–95. https://doi.org/10.1109/MCOMSTD.201.2100023
Davis BD, Mason JC, Anwar M (2020) Vulnerability studies and security postures of IoT devices: A smart home case study. IEEE Internet Things J 7(10):10102–10110. https://doi.org/10.1109/JIoT.2020.2983983
Fourati Hasna, Maaloul Rihab, Chaari Lamia (2021) A survey of 5G network systems: challenges and machine learning approaches. Int J Mach Learn Cyberne 12(2):385–431. https://doi.org/10.1007/s13042-020-01178-4
Gheisari Mehdi, Najafabadi HE, Alzubi JA, Gao J, Wang G, Abbasi AA et al (2021) OBPP: an ontology-based framework for privacy-preserving in IoT-based smart city. Future Generation Computer Systems. 123:1–13. https://doi.org/10.1016/j.future.2021.01.028
Giordani M, Polese M, Mezzavilla M, Rangan S, Zorzi M (2020) Toward 6G networks: use cases and technologies. IEEE Commun Mag 58(3):55–61. https://doi.org/10.1109/MCOM.001.1900411
Jin B, Xiaojie Xu (2024) Forecasting wholesale prices of yellow corn through the Gaussian process regression. Neural Comput Appl 36(15):8693–8710. https://doi.org/10.1016/j.meaene.2024.100001
Jin B, Xu X (2024) Wholesale price forecasts of green grams using the neural network[J]. As J Econo Bank. https://doi.org/10.1108/AJEB-01-2024-0007
Jin B, Xu X (2024b) Pre-owned housing price index forecasts using Gaussian process regressions [J]. J Model Manag. https://doi.org/10.1108/JM2-12-2023-0315
Kim Jin Ho (2021) 6G and Internet of Things: a survey. J Manage Analyti 8(2):316–332. https://doi.org/10.1080/23270012.2021.1882350
Li Yang, Feng Juan Lu, Xiuli Liu Qiang (2019) Design of security monitoring system for smart home based on internet of things. Modern Electr Technol 42(8):55–58
Google Scholar
Liu Y, Zhang J, Zhan J (2021) Privacy protection for fog computing and the internet of things data based on blockchain. Clust Comput 24(2):1331–1345. https://doi.org/10.1007/s10586-020-03190-3
Mafakheri B, Heider-Aviet A, Riggio R, Goratti L (2021) Smart contracts in the 5G roaming architecture: the fusion of blockchain with 5G networks. IEEE Commun Mag 59(3):77–83. https://doi.org/10.1109/MCOM.001.2000857
McLaney Elizabeth (2022) A framework for interprofessional team collaboration in a hospital setting: advancing team competencies and behaviors. Healthcare Manag Forum 35:2. https://doi.org/10.1177/0840470421106358
Meneghello F, Calore M, Zucchetto D, Polese M, Zanella A (2019) IoT: Internet of threats? A survey of practical security vulnerabilities in real IoT devices. IEEE Internet Things J 6(5):8182–8201. https://doi.org/10.1109/JIoT.2019.2935189
Nguyen V-L, Lin P-C, Cheng B-C, Hwang R-H, Lin Y-D (2021) Security and privacy for 6G: A survey on prospective technologies and challenges. IEEE Commun Surv Tutorials 23(4):2384–2428. https://doi.org/10.1109/COMST.2021.3108618
Rajesh Sreeja, Paul V, Menon VG, Khosravi MR (2019) A secure and efficient lightweight symmetric encryption scheme for transfer of text files between embedded IoT devices. Symmetry 11(2):293. https://doi.org/10.3390/sym11020293
Satyam Dwivedi, Shreevastav Ritesh, Munier Florent, Nygren Johannes, Siomina Iana, Lyazidi Yazid et al (2021) Positioning in 5G networks. IEEE Commun Mag 59(11):38–44. https://doi.org/10.1109/MCOM.011.2100091
Stergiou CL, Psannis KE, Gupta BB (2020) IoT-based big data secure management in the fog over a 6G wireless network. IEEE Internet Things J 8(7):5164–5171. https://doi.org/10.1109/JIoT.2020.3033131
Tao Han, de Igor L, Ribeiro Naercio Magaia, Preto Joao, Afonso H, Segundo Fontes N, Antonio Roberto L et al (2021) Emerging drone trends for blockchain-based 5G networks: open issues and future perspectives. IEEE Network 35(1):38–43. https://doi.org/10.1109/MNET.011.2000151
Ullo Silvia Liberata, Sinha Ganesh Ram (2020) Advances in smart environment monitoring systems using IoT and sensors. Sensors 20(11):3113. https://doi.org/10.3390/s20113113
Wang M (2020) Security and privacy in 6G networks: New areas and new challenges. Digital Commun Netw 6(3):281–291
Wen Miaowen, Li Qiang, Kim Kyeong Jin, Lopez-Perez David, Dobre Octavia A, Vincent Poor H et al (2021) Private 5G networks: concepts, architectures, and research landscape. IEEE J Sel Top Signal Proce 16(1):7–25. https://doi.org/10.1109/JSTSP.2021.3137669
Yadawad R, Kulkarni UP, Alzubi JA (2024) Auto-metric graph neural network for attack detection on IoT-based smart environment and secure data transmission using advanced wild horse standard encryption method. Int J Comp Netw Inf Security 16(3):1–15. https://doi.org/10.5815/ijcnis.2024.03.01
Yan Lin, Zeng M, Ren S, Luo Z (2021) Encrypted traffic identification by fusing softmax classifier with its angular margin variant. IEICE Trans Inf Syst 104(4):517–520. https://doi.org/10.1587/transinf.2020EDL8130
Yang H, Alphones A, Xiong Z, Niyato D, Zhao J, Kaishun Wu (2020) Artificial-intelligence-enabled intelligent 6G networks. IEEE Network 34(6):272–280. https://doi.org/10.1109/MNET.011.2000195
Yao Xuanxia, Farha Fadi, Li Rongyang, Psychoula Ismini, Chen Liming, Ning Huansheng (2021) Security and privacy issues of physical objects in the IoT: challenges and opportunities. Digital Commun Netw 7(3):373–384. https://doi.org/10.1016/j.dcan.2020.09.001
Zhang S (2019) An overview of network slicing for 5G. IEEE Wirel Commun 26(3):111–117. https://doi.org/10.1109/MWC.2019.1800234
Zhenyu W, Yang G, Shaoqing Li, Shen H, Ding D (2022) Design of Efficient Anonymous Identity Authentication Protocol for Lightweight IoT Devices. Journal of Communications 43(7):49–61. https://doi.org/10.11959/j.issn.1000-436x.2022125
Download references
This work was supported by the Shandong Province Art Key Project (L2021Q07080186).
Author information
Authors and affiliations.
College of Information Engineering, Weifang Engineering Vocational College, Qingzhou, 262500, Shandong, China
Hailin Liu, Yuanyuan Wang & Fengqi Jia
You can also search for this author in PubMed Google Scholar
Corresponding author
Correspondence to Hailin Liu .
Ethics declarations
Conflicts of interest.
The authors declare that there are no conflicts of interest regarding the publication of this article.
Additional information
Publisher's note.
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
Reprints and permissions
About this article
Liu, H., Wang, Y. & Jia, F. Security and Privacy Protection of Internet of Things Devices in 6G Networks. Int J Syst Assur Eng Manag (2024). https://doi.org/10.1007/s13198-024-02512-7
Download citation
Received : 04 July 2024
Revised : 27 August 2024
Accepted : 08 September 2024
Published : 24 September 2024
DOI : https://doi.org/10.1007/s13198-024-02512-7
Share this article
Anyone you share the following link with will be able to read this content:
Sorry, a shareable link is not currently available for this article.
Provided by the Springer Nature SharedIt content-sharing initiative
- IoT Security
- Privacy Protection
- Device Authentication
- Malware Detection
- Find a journal
- Publish with us
- Track your research

IMAGES
VIDEO
COMMENTS
2. Prepare your paper for submission. Download our get published quick guide opens in new tab/window, which outlines the essential steps in preparing a paper.(This is also available in Chinese opens in new tab/window).It is very important that you stick to the specific "guide for authors" of the journal to which you are submitting.
Submissions must also include images, captions, and sourcing as per the style guide. Failure to follow these guidelines will result in your submission being archived without response. Please be aware that a small fraction of submissions are chosen for publication. Submissions welcome to the editors via [email protected].
3. Submit and revise. You can submit to most Elsevier journals using our online systems. The system you use will depend on the journal to which you submit. You can access the relevant submission system via the "submit your paper" link on the Elsevier.com journal homepage of your chosen journal. Alternatively, if you have been invited to submit ...
Sun and Linton (2014), Hierons (2016) and Craig (2010) offer useful discussions on the subject of "desk rejections.". 4. Make a good first impression with your title and abstract. The title and abstract are incredibly important components of a manuscript as they are the first elements a journal editor sees.
References should be included. Figures should not be copyrighted. Please submit your work to [email protected]. Note: After initial submission, writers whose articles are being considered for publication may be asked to resubmit their articles according to more specific guidelines. MIT International Review.
As an Elsevier author, when submitting your article, you can choose to store your data in a repository like Mendeley Data, in order to make your dataset independently citable, and link it with your article. You can also choose to submit a brief, peer-reviewed data article. Your data article will be published in the dedicated, open access ...
Read more. - Electronic submission. - Reviewing and acceptance. - Managing copyright - The "MyPublication" process. - Copy editing and language polishing. - Data processing and type setting. - Article Tracking. - Checking your article: proofing procedure. - e.Proofing - Makes editing easy!
Step 1: Choosing a journal. Choosing which journal to publish your research paper in is one of the most significant decisions you have to make as a researcher. Where you decide to submit your work can make a big difference to the reach and impact your research has. It's important to take your time to consider your options carefully and ...
Once you think your manuscript is ready for submission, the next important step is to read the aims and scope of the journals in your target research area. Doing so will improve the chances of having your manuscript accepted for publishing. Submit a cover letter with the manuscript. Never underestimate the importance of a cover letter addressed ...
Call for papers in your subject area. Journals regularly 'call for papers', asking for submissions within a particular field or topic. Answering these is a great way to get published, making sure your research fits the journal's aims and scope. Simply select your subject area with our handy tool to get started. Search current calls for ...
The publication process explained. The path to publication can be unsettling when you're unsure what's happening with your paper. Learn about staple journal workflows to see the detailed steps required for ensuring a rigorous and ethical publication. Your team has prepared the paper, written a cover letter and completed the submission form.
The introduction section should be approximately three to five paragraphs in length. Look at examples from your target journal to decide the appropriate length. This section should include the elements shown in Fig. 1. Begin with a general context, narrowing to the specific focus of the paper.
It will give your article additional visibility. Our submission systems will offer the option to include your funding source in a standardized way. In most cases you will be able to choose your funder from the given list. Otherwise, please add it manually. The funding information will be published as searchable meta-data for the accepted article.
To Publish a Research Paper follow the guide below: Conduct original research: Conduct thorough research on a specific topic or problem. Collect data, analyze it, and draw conclusions based on your findings. Write the paper: Write a detailed paper describing your research.
A. Yes, instead of giving the volume and page number, you can give the paper's DOI at the end of the citation. For example, Nature papers should be cited in the form; Author (s) Nature advance ...
The introduction section should be approximately three to five paragraphs in length. Look at examples from your target journal to decide the appropriate length. This section should include the elements shown in Fig. 1. Begin with a general context, narrowing to the specific focus of the paper.
3. Submit your article according to the journal's submission guidelines. Go to the "author's guide" (or similar) on the journal's website to review its submission requirements. Once you are satisfied that your paper meets all of the guidelines, submit the paper through the appropriate channels.
Beyond this, the title should indicate the research methodology and topic of the paper. The abstract should provide a summary of the objective, methods, results, and significance of the research. Most researchers are likely to find published papers through an electronic search (either via subject databases, or search engines such as Google).
International History: The journal encourages manuscript submissions in the form of scholarly essays on all aspects of international history, using any historical approach and historical research. The journal welcomes manuscripts that draw on political, social, diplomatic, cultural, gender, race, military, and economic histories that are ...
Ensure that your submission package is complete. Understand the submission process/system used for publishing in an international journal and find out whom to contact and how in case you have queries. Write a compelling cover letter. This document is probably the first submission item that a journal editor will read and can influence the fate ...
Before submitting your paper, it is wise to revise it and correct any factual errors and knowledge gaps that might have occurred. Step 4: Submit Your Paper ... To publish a research paper in an international journal, it is necessary to research international journals that specialise in your field. Your paper should adhere to all international ...
Submit your Research. Articles are published rapidly as soon as they are accepted, after passing a series of prepublication checks to assess originality, readability, author eligibility, and compliance with Stosunki Międzynarodowe - International Relations's policies and ethical guidelines. Peer review by invited experts, suggested by the ...
Choose the journal in which you want to publish the paper. Check the sample paper and "Instruction to Authors" or "Author's Guide" of that particular journal. Prepare your manuscript according to the format. Every journal article follows a specific format, such as Abstract, Introduction, Methods, Results, Discussion, Conclusion, and ...
Small, self-contained research projects; Development of research methodology; Development of new research technology; A doctoral student may not apply for an R03 grant to support thesis or dissertation research. An R03 award may be used to assist students who are pursuing dissertation studies when the work is within the scope of the R03 award.
With the gradual maturity of 6G (sixth-generation mobile communication network) technology, the security and privacy protection of Internet of Things (IoT) devices have become the research focus areas. This paper discusses how to improve the security and privacy protection level of IoT devices in a 6G network environment to deal with the low success rate of device authentication, inaccurate ...